Cyber Security: When Crime Goes Online
As life moves increasingly online, so do crime and fraud. This week, we uncover some personal secrets from a supposedly blank hard drive, find out how hackers can use baby monitors to spy on people and hear about the next generation of passwords. Plus, news of how Zika virus could be used to combat brain cancer and plans to build an even bigger, stronger particle accelerator.
In this episode

00:51 - Timed meals could prevent jetlag
Timed meals could prevent jetlag
with Jonathan Johnston, University of Surrey
Anyone who works a night shift or travels across time zones knows exactly what jetlag is. Your body wants to be awake or asleep at all the wrong times. The reason this happens is almost every cell in the body has a chemical clock ticking inside it… This is used to link the metabolism of the cell to the demands of the day. Upset that rhythm and... you know the consequences. The assemblage of clocks in the body all fall into step with a master clock in the brain. But now scientists at the University of Surrey have found that these "peripheral clocks" are also sensitive to other cues as well, like when you eat your dinner. And it might be possible to stop some of the side effects of shift work by altering when we eat. Jonathan Johnston spoke to Chris Smith about the work…
Jonathan - We now know that actually we have loads of clocks throughout our bodies. Within mammals, including humans, we have a so-called ‘master clock’ that sits at the base of the brain. This latches on to the light/dark cycle to enable our bodies to be synchronised to the lighting environment in the outside world, but we have other clocks pretty much throughout the entirety of the body. We think that these so-called ‘peripheral clocks’ that exist outside of the brain regulate local function within the tissues that they reside in.
Chris - Are they in some way linked to that master clock in the brain?
Jonathan - Yes, that’s right. In a normal situation, all the clocks in the body are in sync with one another. We know that one of the main functions of the master clock in the brain is to maintain the synchrony between all the clocks elsewhere in the body by nerve outputs, by hormonal outputs and, to some degree, by regulating behaviour as well.
Chris - So what didn’t we know?
Jonathan - What we didn’t know was how we can use things like meal timing to synchronise clocks outside of the brain. We’ve known for a while that there’s a really intimate link between circadian body clocks and metabolism. If you eat a particular meal during the daytime compared to at the nighttime, that same meal will give you much higher levels of blood sugar and blood fat after the meal if you eat the meal at night.
So we’ve known that your response to food is dependent on what time of day you eat, but we haven’t really looked in much detail at the other way round - how the time at which you eat might be able to synchronise your body clock system.
Chris - And that’s what you were doing in this paper?
Jonathan - That’s exactly what we were doing, yes.
Chris - How?
Jonathan - We used a very intensive human protocol and for the first part of the laboratory protocol we had them on fixed sleep/wake and light schedules within the laboratory. We gave them an early breakfast half an hour after they woke up, a lunch five hours after the breakfast, and then a dinner five hours after the lunch. So all their meals, if you like, were squashed toward the early part of day.
They then had another six days in the lab, and for those six days they had the same lighting and sleeping schedule as they had previously. The only difference was that each of their three meals was delayed by five hours. So they had a late breakfast, a late lunch, and a late dinner, which enabled us to then measure the effects of this late meal on their internal circadian system.
Chris - What was the pattern?
Jonathan - I think the most striking result was that the five hour delay in the mealtimes caused a five hour delay in our natural rhythms of blood sugar concentration. So clearly, our mechanisms for controlling blood sugar were able to be re-synchronised with food.
Chris - Why does that matter?
Jonathan - Because we know that a lot of people experience elements of what we call circadian desynchrony.
Chris - So jetlag?
Jonathan - Jetlag is a classic example. Another one would be people doing shiftwork. People for a number of years now have been looking at how we can use things such as light or a melatonin tablet to try and resynchronise these rhythms. The problem there is that we know that light and melatonin are very effective, if given at the right time of day, in resynchronising the master clock within the brain but they probably don’t have much direct effect on our metabolic rhythms.
So what this means now is that we know shift workers have a high association with things like obesity, metabolic disease, and cardiovascular disease. What we hope in the future is that if we can incorporate timed meals as a strategy for helping these people, that will then reduce some of their long term risk factors for these very important diseases.
05:49 - Could Zika virus be used to fight cancer?
Could Zika virus be used to fight cancer?
with Ian Goodfellow, University of Cambridge, Harry Bulstrode, Addenbrooke's Hospital
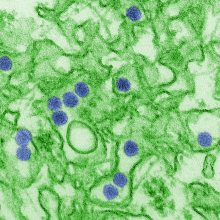
The 2014 outbreak of Zika virus in Brazil was heralded by a dramatic increase in cases of babies born with microcephaly, a condition characterised by an undersized head and brain, caused by infection during pregnancy. But why the virus targets the nervous system wasn't known. Now scientists at Cambridge University have uncovered the answer and may have serendipitously discovered a means to make safer Zika vaccines as well as a treatment for brain cancer. Taking up the story with Chris Smith was virologist Ian Goodfellow...
Ian - Zika infection during pregnancy can lead to this increased occurrence of microcephaly - children with small heads essentially. We got involved in a collaborative project with some researchers here at the Cancer Research Institute to try to understand why Zika virus causes microcephaly, and essentially, what we found was that Zika virus likes to grow in cells that express a protein known as MSI1. This protein is a regulator of genes involved in neural development. Zika virus likes to infect these neuronal progenitor cells because they have high levels of this protein and, by doing so, it kills those cells.
In fact, if we take normal laboratory cells that don’t express this protein and we try to infect them with Zika, it doesn’t really replicate very well. But if we introduce this protein and then infect them with Zika virus, the virus will replicate very well and will also kill the cells.
Chris - What put you onto the fact that Zika is hungry for this protein in the first place?
Ian - Our collaborators at the C.R.I. identified a family where there were two children born with microcephaly and it turned out these two children had a mutation in this gene (MSI1). This put us onto the idea that maybe MSI1 might be involved in the development of microcephaly. MSI1 is a key regulator for other genes in neuronal development, so when the virus infects those cells it also inhibits the ability of that protein to function so the expression of genes involved in normal brain development is altered by the virus. But, at the same time, it’s also trying to kill those cells it infects.
Chris - The Zika virus comes in, it soaks up this factor in the cells that would normally be necessary for those cells to develop normally as nerve cells. Uses them to encourage the virus to grow and, therefore, pushes the cells off target, they turn into turn into the wrong thing and die, but you end up with Zika virus at the end of it?
Ian - Absolutely, that’s exactly what happens. The one point I’d make as well is that at this point we still don’t know what that protein is doing in the virus life cycle. We know it’s important, but we don’t know exactly what it’s doing. But it is possible potentially in the future if we were able to make a mutated virus that didn’t bind to this MSI1 protein and, therefore, didn’t replicate in the neuronal progenitor cells but does generate a good immune response, we could use that as a potential vaccine and this is something we would like to explore in the future.
Tim - Ian Goodfellow, who wants to prevent Zika infections. But surprisingly, Zika actually might also be useful. Some researchers who are interested in exploiting Zika's tendency to kill brain cells by using it as a weapon to treat certain cancers in the nervous system...
Harry - My name is Harry Bulstrode; I’m a clinical lecturer in the Neurosurgery Department here at Addenbrooke’s Hospital, Cambridge.
The project that I’m working on is based on brain tumours, particularly nasty brain tumours called a glioblastoma. Glioblastomas grow and invade into brain and we operate on these tumours, and remove the tumours, but they invariably recur. So they come back and typically these patients only survive a few months or maybe a year or two, so it’s really a devastating diagnosis.
Part of the reason that these tumours are so nasty, we think, is that they include a population of stem cells - what we call glioma stem cells. When we look at these cells we find that they behave really very similarly to the stem cells in a baby’s brain that cause rapid growth of the brain in the womb. So, as a baby, you need your stem cells to divide and grow very, very quickly and it seems like the cancer is using the same programme that those baby stem cells are using to grow in the adult when it should be switched off.
It seems that the Zika virus is attacking the stem cells in the baby’s brain and that’s why it’s causing small brains and failure of brain development in the baby. It seems that the Zika virus doesn’t attack normal adult brain very much because adults can get Zika virus without becoming severely ill. What that makes us wonder is that whether we might have here a virus that will specifically attack the stem cell population that shouldn’t be present in the adult but is present in adults with brain tumours.
Chris - If you kill off those stem cells using Zika virus, which you might not be able to get at using surgery because you might end up doing devastating damage to the person’s brain to get all of them out, the virus will, effectively, ferret them out for you and where it hits healthy brain tissue again, it will just switch off?
Harry - Yeah. That’s the hope that after any operation for these tumours, there are always a few cells left behind because they’ve invaded so widely in the brain. In fact, in the 1930s when these operations were first being done, people used to cut out half the brain to try and cure these patients, the tumour would still come back in the other half of the brain. So these patients were left disabled and the tumours still come back. What’s clear is that we need to find a new way to get at these stem cells that are hiding in normal brain, and it seems like Zika might offer us some ideas about how to do that.
Chris - How do you envisage actually starting?
Harry - We can grow the stem cells we’re interested in - both the baby stem cells and also the tumour stem cells. We can grow those in dishes and then we can infect them and see what happens. What we can then do is think about developing a mouse model where mice with brain tumours are then treated with the Zika virus to see if the Zika virus can attack the brain tumours in the mouse, and we can begin to see the effect on tumour versus the effect on normal brain.

12:38 - Touching the void: virtual reality
Touching the void: virtual reality
with Peter Cowley, Angel Investorys
Would you ever want to feel like you’re at the centre of a video game? Virtual reality is getting closer and closer to real life thanks to the introduction of touch sensors. Tech expert and Angel Investor Peter Cowley spoke to TImothy Revell...
Peter - Virtual reality is the concept where the image that one is viewing is completely computer generated. So it’s generated by graphics or it’s generated by one of these new 360 degree cameras.
Mixed reality, which is a term that’s disappearing gradually, is where you mix the actual scene around you as a human being with some computer generated scene. Augmented reality has not got the ability to interact with that so that in augmented reality you can’t necessarily push something and it will move. But augmented reality is the future where you’re interacting with something else in the environment.
Tim - Some people talk about starting to introduce touch into this equation. How does that work?
Peter - We’re using sight and sound and this is adding a third sense. So this is where some part of your body, whether it’s the chest or the arm, fingers, etc., is experiencing something which is mechanical, so it feels like you’re actually touching some subject or some object. That’s come about because of a whole stack of new technologies like these micro accelerometers in your phones etc., have all got very cheap, and connectivity, so it’s been put together to provide devices which are not necessarily on your skin - a thimble might do it, but also blowing air. There’s a great video on the internet of a butterfly floating around on somebody’s arm which is done by puffs of air from various directions hitting the skin of the arm.
Tim - Besides this being really cool, is this useful in some way?
Peter - Gaming has used it for a long time. In fact, if you go back further still, the stick shakers which were put on the vulcan bomber in the 50s if it was about to stall, that’s feedback into the system.
There’s a lot of new applications - for instance medical. I saw a medical robotics company in Cambridge on Friday which is allowing the surgeon to feel the tissue inside the body while he’s operating on it. Training for aircraft maintenance, military, etc. There’s a new one as well in teaching where you can get the students to understand something better like a three dimensional image if they can feel it at the same time as see it.
Tim - In terms of surgery - is this for robotic surgery? Could you also imagine a situation where you were practicing on a body that doesn’t even exist yet but you’re getting the same sorts of feelings you might do when you’re a surgeon?
Peter - Absolutely. For training purposes you could be inside the body doing things so that you get a feel for what’s it’s going to be like when you’ve got a real human being in front of you.
Tim - How far away is this from becoming normal or something we can actually use?
Peter - If you remember the Microsoft Kinect, which was a gaming device, that’s being used for the gait of horses or the gait of people, so applications come out of other things. At the moment it’s definitely strongly used in gaming. But the killer app, if there is a killer app, hasn’t been found yet. There’s a huge amount of technology and a huge amount of investment going into VR and AR headsets and the world will work out what the best use is for it, but it’s not that clear for me at the moment.
15:56 - Bigger and stronger: the next Large Hadron Collider
Bigger and stronger: the next Large Hadron Collider
with Professor Carsten Welsch, University of Liverpool
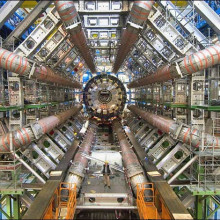
At the end of May, scientists from all over the world met in Berlin to discuss the successor to the Large Hadron Collider, the particle accelerator at CERN. This one they’re calling the Future Circular Collider, or FCC, which will be up to three times larger and seven times more powerful than the current LHC and aims to simulate energy levels much closer to those seen during the ‘Big Bang’. Tom Crawford heard about the project from physicist Carsten Welsch at the University of Liverpool…
Carsten - The fundamental driving question of all of this is why: why are we; why is universe the way it is; why do the fundamental forces behave in the way that they behave? A future collider can give us the insight that currently cannot be gained by using any of the facilities on Earth because we are limited in the ultimate energy of these colliders.
Tom - Can we not upgrade or extend the current Large Hadron Collider that we have?
Carsten - The fundamental problem is we need to look into what limits the performance of the current Large Hadron Collider. There are a few limitations and one of them is the ultimate achievable energy. Now the energy of a particle beam is provided to the particles by means of radio frequency power which is pumped into the accelerator and then transferred over to the beam. In order to keep that beam on a circular path you need magnets. There's simply not the technology available to bend a higher energy particle beam around the 27 kilometre circumference of the LHC so, at the moment, we want to go to higher beam energies. We need much stronger magnets in the existing tunnel or we need a larger tunnel in order to be able to store that kind of high energy particle beam.
Tom - Looking back at what we’ve learnt in the past from the LHC and from these kinds of experiments - of course there was the discovery of the Higgs Boson particle which is huge - but beyond the physics and understanding are there any other applications in everyday life?
Carsten - Absolutely. If you look at past colliders, every single particle collider lead to a breakthrough in our understanding of nature. It is not unlikely that there will be similar discoveries also in that energy range.
In terms of more tangible applications immediately for society, if you look back again in the history of particle physics, the impact on society can’t be overstated. For example, the internet itself was basically a spinoff from particle physics collaboration and what would we be today without the internet and mobile communications?
The magnets we talked about before are used nowadays routinely in hospitals for NMR diagnostics. So having access to better magnet technologies, even higher field strengths, would increase the resolution of such medical diagnostics automatically. The technologies that will be developed along the conceptual design of this machine will lead to breakthroughs that also impact on our lives every single day.
Tom - What is the main aim then of the FCC project?
Carsten - At the moment there’s an international community who looks into a conceptual design report. What will be required in order to build such a machine.
Tom - So it’s like you’re planning for the plan in some sense?
Carsten - Absolutely. At the moment the LHC has an expected lifetime of at least 20 years from now. So if you look at these timescales then the construction of the next machine would already take me pretty close to my retirement age. We need to engage the next generation of scientists, so these are really school kids today, to think about the questions we don’t have answers for at the moment. That they consider a career in science and also develop technologies that will benefit everyday life in the future.

Another Earth?
with Professor Stephen Hawking, Cambridge University; Garik Israelian, Starmus Festival; Claude Nicollier, European Space Agency; Simon Evetts, Blue Abyss
Could you imagine living elsewhere? We’re not talking about a new home or town but a different planet! Recently, Professor Stephen Hawking has said that we have 100 years left to colonise a new planet. He, along with other eminent scientists will be speaking at Starmus Festival in Trondheim later this month. This five day festival is a celebration of science and music, and it’ll be at Starmus where Professor Hawking will reveal just what the problem is. In the meantime, Izzie Clarke went to an event at the Royal Society in May to investigate what needs to be done to find an alternative Earth…
Stephen - I strongly believe we should start seeking alternative planets for possible habitation.
Izzie - Even from Professor Stephen Hawking himself, it sounds like an impossible challenge. Can we really find and colonise a new planet within the next century? With climate change and the global population continuing to increase, is there a plan - or planet - B? I spoke to astronomer and Director of Starmus Festival, Garik Israelian to found out what conditions we’d need to survive on an alternative Earth.
Garik - We were part of the evolution for millions of years. It’s very deep in our genes to have the daylight that we have, the magnetic field of the Earth that we have. We would need the same gravity, so we don’t really know, if you change those conditions slightly - lets say 10% of the magnetic field, 10% of the daylight - what will happen to us? How are we going to evolve as creatures?
Izzie - Are there any possible planets that we might be able to relocate to in the next 100 years?
Garik - No. We don’t know any now. The only thing that astronomers find from time to time are planets where you can have liquid water. But we have no idea about magnetic fields in those planets; we have no idea about atmospheres so all these parameters that we have for the Earth. But I don’t think that having a planet with the mass of the Earth and with liquid water is enough.
Izzie - So more research needs to be done into finding an alternative Earth. Earlier on in the year, scientists from the University of Cambridge found signs of water on a planet within Trappist 1, a planetary system 39 light years away. That’s quite a long way to go without knowing other environmental factors! But imagine if we had found the perfect planet - how do we get there? What, in terms of technology, is holding us back?
Claude - I’m Claude Nicollier. I was a European Space Agency astronaut for 25 years. The two major problems in technology development for the next few decades for going to the solar system will be protection against radiation and the proper propulsion system.
The problem is, if you go outside of the vicinity of the Earth towards the Moon, or Mars, or satellites of Jupiter or Saturn, we need to protect the crew against radiation. Once we are on the surface of another celestial body, we can build habitats where there is protection. If we are on Mars, we can use Mars material to cover the habitat so that we are protected, to a certain degree, against radiation.
For the rest we need, of course, propulsion systems that allow us to go from one place to another in the solar system using something other than chemical propulsion. Chemical propulsion doesn’t give us enough efficiency and capability to travel.
Izzie - Do you know of any further work that’s being done to reach that?
Claude - Lots of testing is being done on nuclear propulsion or, lets say, was done in the 60s mainly and then it was kind of abandoned. We are starting now again to look at new propulsion systems and once you are in space you can use electric propulsion where you ionise a material, then you accelerate the ions using an electric field. The problem with electric propulsion or what’s very efficient, is the thrust is very low. So you cannot leave the surface of a celestial body, be it the Earth, or Mars, or any other body in the solar system using electrical propulsion. But to go from one place to another, if you have enough time, you can do it.
Izzie - It’s safe to say we need to improve our propulsion systems and radiation protection. But what about the human body? Can it actually cope with such a long journey? I spoke to Simon Evetts, a space physiologist who’s creating the first commercial astronaut training centre Blue Abyss…
Simon - When we’re in space and gravity is taken away from us we have less need to contract our muscles. There aren’t heavy things to lift up and we don’t move our heavy body around, so our muscles and our bones decondition - they wither if you like.
Izzie - What are some of the other factors that will affect us living in space?
Simon - Radiation is currently one of the showstoppers, whether it be galactic cosmic radiation or solar flares. High energy particles can hit the body and hit the cells, and these can damage and mutate cells increasing the risk of cancer which is, of course, something we want to avoid. We see reductions in immune capability that occur over long periods in space. All of these things add up to basically deconditioning and degrading the body and our physicality.
Izzie - Can we live in deep space for a long period of time?
Simon - Using the same systems that we have now, then I would say no. It’s very unlikely that we would do so because the body de-conditions so much and the individuals involved would be in a weak state when they arrived at the planet, X number of months or years away.
What we need ideally is, rather than a number of systems and a number of devices to be able to help us, we need to take gravity with us. So we’re talking about spinning space ships, we’re talking about human centrifuges in space. Because if we’ve got artifical gravity with us then all of our systems are being affected and stimulated in the same way that we tend to find on Earth.
Izzie - Right. So all we have to do in the next 100 years is to find a new planet with the same mass, atmosphere, and magnetic field. Develop a new propulsion system and, ideally, have a spacecraft that generates artificial gravity and protects us against radiation!
Stephen - We are running out of space on Earth and we need to break through the technological limitations preventing us living elsewhere in the universe. I am not alone in this view and many of my colleagues will make further comments on this at Starmus next month.

27:27 - Secrets in your hard drive
Secrets in your hard drive
with Graham Ryme, Computer Laboratory in Cambridge
What do people tend to do with an old computer? Half of UK owners take their old machines to the tip, which amounts to millions of dumped computers. But what about the data that was on those computers? Most people believe that, if you delete something, it’s gone. Unfortunately, it hasn’t, as Izzie Clarke found out...
Izzie - Have you ever sold an old laptop? If so, you probably made sure you deleted all your files before you parted ways. But how can you be sure that all your data was wiped from your device? I’ve got my hands on a used hard drive, the data storage device on a computer and all the files from the previous owner have, apparently, been deleted. This is a process called formating. It’s a simple function on your computer that gets rid of all of your data so there shouldn’t be any information left on here - right?
Well, to double check, Graham Rymer from the Computer Laboratory in Cambridge is going to run a few tests to see if the hard drive is indeed empty…
The hard drive from a computer is usually the size of a paperback book. All of your files and any activity that you do on your computer is recorded there. Graham had about 24 hours to investigate.
So what did you find? I can see loads of different files right in front of me
Graham - There is an element of triage because there’s just so much data available. This chap was a keen photographer…
Izzie - Is that someone’s wedding photos?
Graham - It is. We’ve got hundreds of wedding photos. We have a trip to Paris here and one of the Eiffel Tower. This is the owner of the laptop himself on a skiing holiday.
Izzie - Not only did we have enough archive to track his life over a ten year period but lots of digital photographs have data embedded by the device…
Graham - I can tell that it was taken at about 2.58 pm back in 2009 on the 19th February. A lot of devices now, including the ubiquitous iphone, as well as most cameras, embed GPS data as well.
Izzie - So had this photograph been taken on a smartphone we’d even be able to tell what mountain the previous owner standing on. Date, time and location. But whilst it’s unnerving, there’s only so much damage can be caused knowing this information.
What else were you able to find?
Graham - We have invoices. I expect the most compromising information that we have is this chap’s driving licence.
Izzie - So that’s got his address on there, his date of birth.
Graham - It’s got his signature.
Izzie - And his signature - yeah. Say he had thought that he’d deleted his hard drive, which is effectively what he thinks he’s done, what could happen if this got into the wrong hands?
Graham - It’s limitless. Obviously there’s the potential for identity fraud. There will be files with passwords saved in and perhaps online banking credentials. Anything which you think is safe on your computer that’s not encrypted is not safe in this context. So anything he left lying about on his computer which could be exploited by an attacker for financial gain perhaps is fair game.
Izzie - Encryption is a modern form of cryptography that allows a user to hide information from others. It uses a complex algorithm which turns your data into a series of seemingly random characters. That means it’s unreadable by those without a special key or password which will then unscramble and decrypt your data. But this hard drive isn't encrypted. We were able to find out the previous owner’s signature, home address, and his bank details thanks to that saved invoice. But can a hard drive reveal even more about an owner…
Graham - Your internet history is just a computer file. It’s a little bit tricker and time consuming to extract that sort of information but anything that existed on his computer before it was formatted is potentially discoverable.
Izzie - Whilst it takes longer to find, this means we would be able to access his email account, his contacts, and even passwords to various online accounts. Potentially bank accounts included.
Obviously we’re based here at the Computer Laboratory in Cambridge. You must have access to so many different techniques and so many utensils - how have you been able to retrieve this information?
Graham - Utensil wise, we used an old wooden spoon really. This is free open source software which we used. Normally that hard drive would be plugged into a computer so that’s exactly what I did. I just got a garden variety desktop PC; I took the side off it; I found a spare cable; I was able to read the data straight off that drive. Any attacker with half an hour of googling could learn the same techniques which we’ve used here. Very, very simple technology.
Izzie - That’s quite terrifying. Effectively what we’ve learnt is that by clicking that delete button, your files aren’t actually removed from the hard drive.
Graham - Absolutely not. It’s like having a book and just ripping out the contents page. If you still want to read the book everything’s there. You just can’t jump to the interesting bits straight away. If you want to rifle through it page by page, you can still find all the information and that’s exactly what these fast deleting and formatting techniques do.
Izzie - How do we properly delete our data from a hard drive? Luckily we’ve come across it, but in the wrong hands that could be quite problematic.
Graham - The only way to defend against this is to overwrite every single part of the disc. Going back to that analogy that would be going through your book quite painstakingly over many, many hours and tipp-exing over every single letter in the book. Obviously, people don’t like to do this routinely because it takes quite a long time but it’s something you might consider doing before you go to sell a laptop. Another defence, which is much, much faster and better for several reasons, is to use encryption. So both OSX has had filevault since the lion version. Since Windows Vista we’ve had bitlocker included. Both these programmes allow you to encrypt volumes on your hard drive and that means that if you ever leave your laptop on a train, if you have your laptop stolen, all that data is useless because it’s just garbled junk on a disk. You don’t have to worry about overwriting the disk afterwards because it’s already junk. Without the password to decrypt it, it’s quite useless to an attacker so I would recommend people seriously consider looking into the encryption options available. This doesn’t have to be a software option. Lots of modern hard drives, especially SOLIS hard drives in business class laptops support encryption as well.

34:26 - Are biometric passwords the future
Are biometric passwords the future
with Nate Lanxon, Bloomberg
A common complaint is that we often have different passwords for different accounts and devices; and to make them secure we have to make these passwords so complicated that then we can’t actually remember them! So it might be music to some people’s ears to hear that the password’s days are numbered because, increasingly, technology is shifting towards using biometric systems instead. But what are these, and are they any better? Nate Lanxon, head of European Technology News at Bloomberg spoke to Chris Smith…
Nate - One of the biggest problems with passwords is that people tend to prefer convenience over security. The most popular password in the world every year is “password,” closely followed by “1,2,3,4,5,6,” because they’re easy to remember. The problem is that with a large percentage of people using such a password it becomes very easy for a hacker to get many thousands of accounts on the assumption that some of them will use these passwords therefore they can get into them very easily. The same is similarly true for just very easy to remember words like summer and people’s names. They’re very easy and they’re hacked with what’s called a dictionary attack. Very easy, very simple, and very common sadly.
Chris - A biometric method of protection - what’s that instead?
Nate - The most commonly used one at the moment that I think most people would be familiar with is a fingerprint sensor on a smartphone. These are becoming increasingly popular since about 2014. A number of manufacturers now use these and essentially what it does is it overrides the need to use a password or a pin because only you have your fingerprint, generally speaking at least. You have the ability to unlock it just by tapping your finger against a phone. You don’t need to remember anything, you just need to be the same as you were when you set it up. You can combine that with a password or with another factor of verification or login - a technology called two factor authentication, so two forms of login together. That increases your level of security enormously and most big companies and large organisations will now try and get people to enable this kind of two factor security if possible.
Chris - Does it actually work like that though Nate? I know Hollywood is Hollywood but certainly I’ve seen films where people chop people’s thumbs off and use them to gain entry to a secure facility. I’ve also heard tell that people have taken photographs of themselves of their eye and then held it up to a security camera and the picture was enough to fool it into thinking it was looking at the individual's real eye.
Nate - It’s true and I will admit I have asked a doctor before now if a finger was cut off, how long would it take before it was useless against unlocking a phone, but I never tend to get a clear answer. The fact is though you are generally right, and away from Hollywood we have seen evidence that the very high resolution of cameras now can take pictures of a person’s iris with enough definition to trick some systems into believing it is the user.
Similar is true of facial recognition where it is looking at a person’s face and unless you’re tracking what’s called depth mapping where you’re not just looking at a photograph of somebody then, again, those can be a little easier to fool. But the key is that most of these systems, at least in the consumer space, they’re often paired with a second factor of authentication for the really important stuff like payment systems and things like that. At the moment they’re there for convenience. Some of them maybe can be fooled if you’re clever enough but they’re not posing a massive risk to security right now.
Chris - What about implementation of this, because it’s not as trivial when we’ve got phones that you can just quite quickly tap in a password into to have some kind of finger scanner or an eye scanner in those devices? Doesn’t this mean we need a regime shift in how all the devices are made and that’s going to take time which will, inevitably, hold things up?
Nate - One hundred percent and that’s exactly why the password is likely to stick around because while all these sensors are becoming more affordable because more people are buying the devices in the high end and that makes the next generation a little cheaper to be implemented in. At the end of the day, not everyone has the budget to buy a smartphone with a fingerprint sensor or an iris scanner in so you need a fallback for the people that don’t have access. That’s why we’ll still have passwords probably for the next 50 years. But it is also hopefully why people may be a little more savvy and aware that “password” in itself is the worst password you can possibly choose.

39:17 - Is the Internet of Things secure?
Is the Internet of Things secure?
with Steven Murdoch, University College London
A world is fast approaching where everything around us is connected to the Internet. Your fridge will shop online for more milk and ice-cream when you run low, your phone will tell your oven that you’re behind schedule on the journey home and to turn the dinner down, and the heating will fire up at the right moment so that the house is already warm when you walk through the door. All of these interconnected devices as referred to as “The Internet of Things”. But with convenience comes risk. And Steven Murdoch, from UCL, spoke to Timothy Revell to explain what we need to watch out for…
Steven - What’s happened with The Internet of Things is that, of course, computers have become cheaper than before and smaller. We can now put them in all sorts of interesting household appliances and to get the full power of computers we want to connect them to the Internet so that they can talk to other computers and talk to us. But the people who are making these home appliances are fairly new to the industry of internet connected things and so they make mistakes.
Tim - What sorts of mistakes are they making? Are the very secure or not really?
Steven - In many cases they are not secure. We’ve seen significant problems; a common one is that the come with default passwords and so anyone who knows the default can log into this computer rather than only the owner. Another one is that the vulnerabilities that people do discover never get fixed because the companies don’t have any way of installing software updates on these computers.
Tim - I remember for while people were worried about smart TVs - what’s that all about?
Steven - Smart TVs are just televisions with computers, but they added in things like cameras and microphones and make useful features like voice recognition. But the way voice recognition worked is it would send your voice up to some other computers run by the manufacturer to work out what is actually being said. The manufacturer - Samsung in this case - warn people not to have private conversations in front of the television, which caused people to be aware of these sorts of risks.
Tim - Yeah, so don’t tell any secrets in your lounge. At the moment you’ve got a device in front of you - what actually is that? It looks a bit like a webcam.
Steven - Yeah. This is a webcam but this one is specifically marketed as a baby monitor and the way I’ve set it up is on my own private network. But what’s happened quite frequently is that people accidently set this up so that anyone on the internet can connect to it and leave it with it’s default password which everyone knows. Then just as I can control it from it’s computer, so if I just press this button you can hear it whirring around.
Tim - That’s the webcam just turning around. This would be used if you’ve got a baby upstairs, instead of having one of those old fashioned walkie talkies, you can see what you’re baby’s doing - if they’re upset or the need some attention?
Steven - Yeah. It’s got an infrared camera; it can see in the dark. It’s got a microphone so you can hear what’s being said and it’s also got a speaker so you can talk to the baby.
Tim - That sounds fantastic. So what can go wrong with one of these internet connected versions?
Steven - What turned out is that there were enough of these that were connected to the internet without any reasonable security and people were able to scan for all of these. Some of these were just dull cctv cameras looking at car parks but other ones actually had children in front of them. One parent discovered that the child was afraid of going to bed at night because there were voices and the parent just thought this was a nightmare. But it turned out that there were some people who were hacking into this camera and then saying things to the child overnight. It was only after quite some time that the parent heard this and worked out what was going on.
Tim - That’s absolutely horrifying to find out that you buy this thing to look after your child but actually someone on the internet’s out exploiting it so how can that be avoided? What should someone do who wants this tech but needs to make sure that their child isn’t being spoken to by a strange person on the internet?
Steven - The standard advice is to do something like change the passwords, which is a good idea, but really I think the government needs to take more responsibility. The Royal Society published a report - I was on the steering committee - which said there should be some way for customers to be able to tell the difference between a device that is designed to be secure and will keep itself secure, from everything else out there which is terrible. I think once that has been put in place, and there are some signs that the National Centre for Cybersecurity will do it, then customers will be in a much better situation of being secured, but not having to jump through ridiculous hoops to do so.

43:47 - Cyber security: policy and protection
Cyber security: policy and protection
with Professor Ross Anderson, University of Cambridge
Evidence is showing that cybercrime is growing very rapidly and, in terms of scale, has overtaken traditional forms of crime and fraud. Ross Anderson is Professor of Security Engineering at Cambridge University; Chris Smith went to see him to hear how large this problem is, what policymakers need to do to stop it, and what other problems maybe laying in wait for us...
Ross - Most crime in Briain is now online. About 1 million British households this year will become victims of traditional property crime such as burglary and car theft. About 4 million households will be victims of fraud scams and abuses of various kinds, the great majority of which are online and electronic.
Chris - What is the relative value of those two crimes though?
Ross - The relative value is probably about the same, but online crime is increasing at a tremendous rate and it does have real psychological effects on people if they become victims of fraud and they’re not believed by their banks, and the police aren’t interested, and everybody just treats as if it was their fault.
Chris - If I come home and someone has broken into my house and ransacked the place, I know exactly what to do. I can phone up the police and they’ll probably send someone round. If I come home and find someone’s been in my bank account online, what do I do?
Ross - What the bank should do is make you good if you’re a victim of fraud; that’s the guidance from the Financial Conduct Authority. But very often banks don’t do that because they’ve got all sorts of small print in their terms and conditions and they’ll say then it’s not their fault, so it must be yours.
Chris - I can’t phone the police then?
Ross - You can phone the police if you like, but the problem is in 2005 and agreement was made between the banks and the police to the effect that fraud should be reported to the banks. As a result, the Home Office has been able to claim for the past dozen years that crime has been falling when, in fact, it’s just been moving on like everything else.
Chris - What can we do about this?
Ross - The police are going to have to put more effort in doing cybercrime enforcement because, at present, the online bad guys know that Britain is basically undefended. You can do cybercrime here, you won’t get pursued and you won’t get arrested except perhaps if the FBI get interested if you defraud Americans.
Chris - So America are much more hot on this than we are?
Ross - America’s much better at cybercrime enforcement than anywhere else. In fact, the American government spends as much on cybercrime enforcement as the next dozen governments put together.
Chris - Given the rate of growth of these sorts of technologies and the interconnectedness of the world we’ve got. The Internet of Things, we’ve got people buying mass produced gadgets from China for example, many of them with very poor security and admin passwords you can’t change, and the admin password is “admin,” for example. What does the government need to do urgently so we’re not continuing to sleepwalk into this nightmare?
Ross - The security problems of the Internet of Things will eventually, I believe, be fixed by players such as the European Union. Europe is already the world’s regulator for privacy, because Washington doesn’t care and nobody else is big enough to matter. I hope that it will become the world’s regulator for safety as well. So when you end up buying things like air conditioners from China or Korea, these will end up having to carry on them a CE mark which means that they comply with all applicable standards. We know have standards for vulnerability management and what that will mean is that you won’t be able to export your air conditioner to Europe unless you’ve got some way of patching vulnerabilities. Once Europe starts enforcing that standard vigorously, we should hopefully be beneficiaries of it even if we have left the EU by then.
Chris - What about transport Ross, because that’s one thing you haven’t mentioned yet? Transports massive - cars, planes and so on. What’s happening with them because they all have computer systems?
Ross - We’re beginning to see in the transport field firstly that some cars have been hacked and have even been driven off the road. What we’re also seeing is that some car makers, such as Tesla, are starting to patch their cars every month so that if vulnerabilities are found they can be fixed.
Chris - By “patch,” you mean the car has got to acquire a new piece of software code to address a problem that’s been identified?
Ross - Yes, that’s right. Your mobile phone and your laptop are typically patched every month. So a new software release come out from Microsoft, or Android, or Apple, or whoever and your laptop or your phone will install that automatically. In future, this is going to have to happen to cars too, and it also provides and opportunity for any safety flaws that arise in self-driving cars to be patched quickly and at skill without having to recall millions and millions of vehicles to the garage to have their software changed.
Chris - Well, that sounds good - what’s not to like?
Ross - The problem is when you start patching stuff every month, you need to maintain a software team which is offay with that particular product. My phone, for example, is a Google Nexus 5x which I bought last year and Google now tells me they’re going to stop security support in September next year, which I find very annoying. I don’t think it’s very good that I’ve only got two years secure life in that product.
If the same thing happens in a car that I buy in two years time, then I will be very annoyed indeed. Because if it becomes necessary to patch a car for it to remain safe, and if you’ve got a ten year old Mercedes and Mr Mercedes suddenly says sorry, it’s too expensive for us to patch cars that are more than ten years old because that would mean we’d have to keep test equipment and engineers current on dozens, and dozens, and dozens of all models, then that would mean that you car has to be taken away and scrapped. If suddenly cars are scrapped after ten years instead of twenty years, that’s going to double the CO2 emissions from the car industry and that’s surely not going to be acceptable.
Chris - What do the government need to do to address all of these very concerning points?
Ross - We did a big study last year for the European Commission because it’s not just cars; it’s medical devices; it’s electrical equipment; it’s all sorts of other things. And the European Union with 500 million people is a big enough market that if they say to Mr Ford, or Mr Samsung, or whoever sorry, unless you meet our standards your products can’t come into our market, then that actually matters. So that, I think, is the place where leverage is going to be applied and we’re going to end up having rules which will simply tell the car makers sorry, you’ve got to keep supplying security patches for 25 years on consumer protection grounds, and environmental grounds. If that’s going to be expensive, you’d better figure out how to do the engineering better, or you’d better have few models, or you’d better hire more engineers - your choice.

50:47 - Why warm up muscles?
Why warm up muscles?
Katie Haylor put this steamy question to Cambridge University's Christof Schwiening.
Christof - Muscles get warm when the contract repetitively, like when you’re running, cycling, or skipping. Yoga produces relatively little heat and the temperature of most muscles will be close to that of your core body temperature whether you’re in a normal room or in one heated to 40 degrees celsius. Scientific investigations into hot yoga provide little evidence that it is much different from normal yoga.
However, passive heating can improve health and make you aerobically fitter. For instance, saunas can produce cardiovascular, skin, and mental health benefits. It is possible that hot yoga may produce some of these effects.
Katie - That’s the “hot” part of hot yoga sorted. What about warming up muscles before a class? What’s going on at a cellular level to make this a good idea?
Christof - The warmer the muscle is, the more force it can produce. The evidence for that is very clear. So if you want to run a fast, short race where maximum power output is needed, you should warm up first.
But warming up is about more than just getting a muscle warm: it’s about increasing blood flow to the muscles and increasing the amount of blood being pumped by the heart. Warming up muscles also changes your general physiology, from the control of blood flow, hormonal background, mental state, neuronal pathways, and energy supply.
As far as yoga is concerned, the main benefit of warming up using movement rather than simple passive heating may well be the changes in neuronal activation. Warming up may well help to relax muscles that would otherwise be partially contracted. It is true that warming can produce small and transient increases in muscle flexibility, but the current view is that it is the training of our nervous systems that produces the biggest improvement in range of motion.
Related Content
- Previous Missions to Mars
- Next Can White Parents Have a Black Baby?










Comments
Add a comment